Three editions. Zero compromises.
Single static binaries. No Docker, no Java, no Python runtime, no shared libraries. Copy it, run it.
For SCIFs, classified networks, and any environment where zero outbound traffic is mandatory.
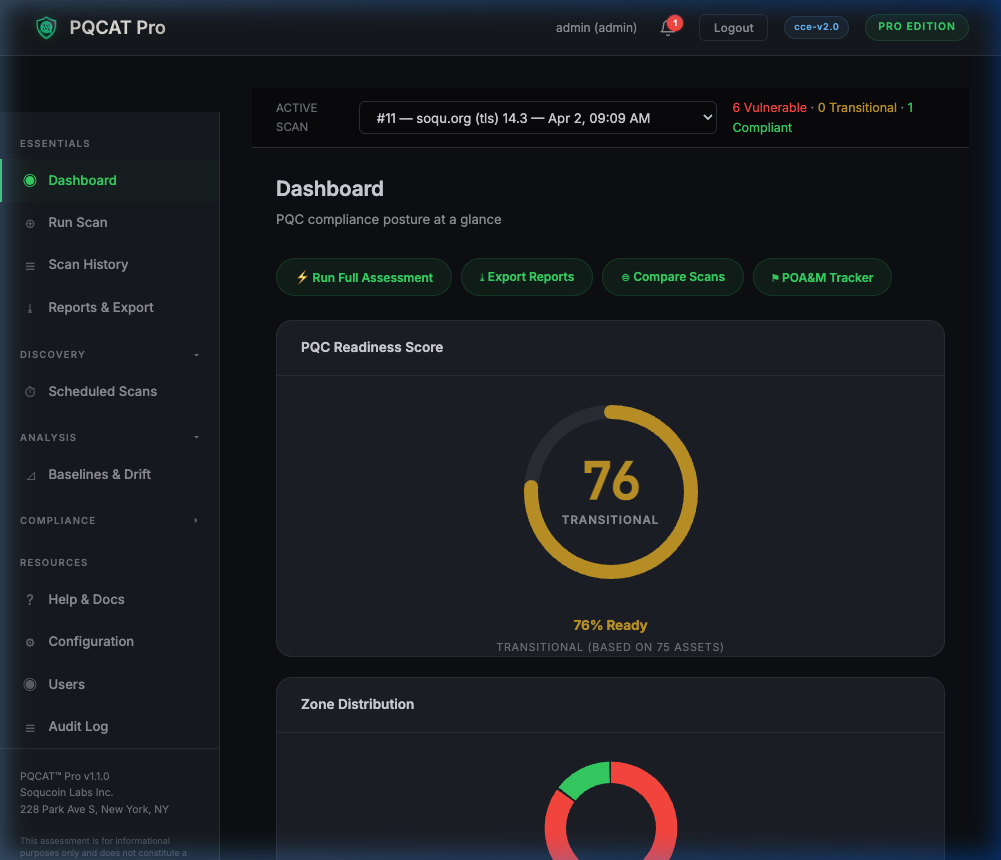
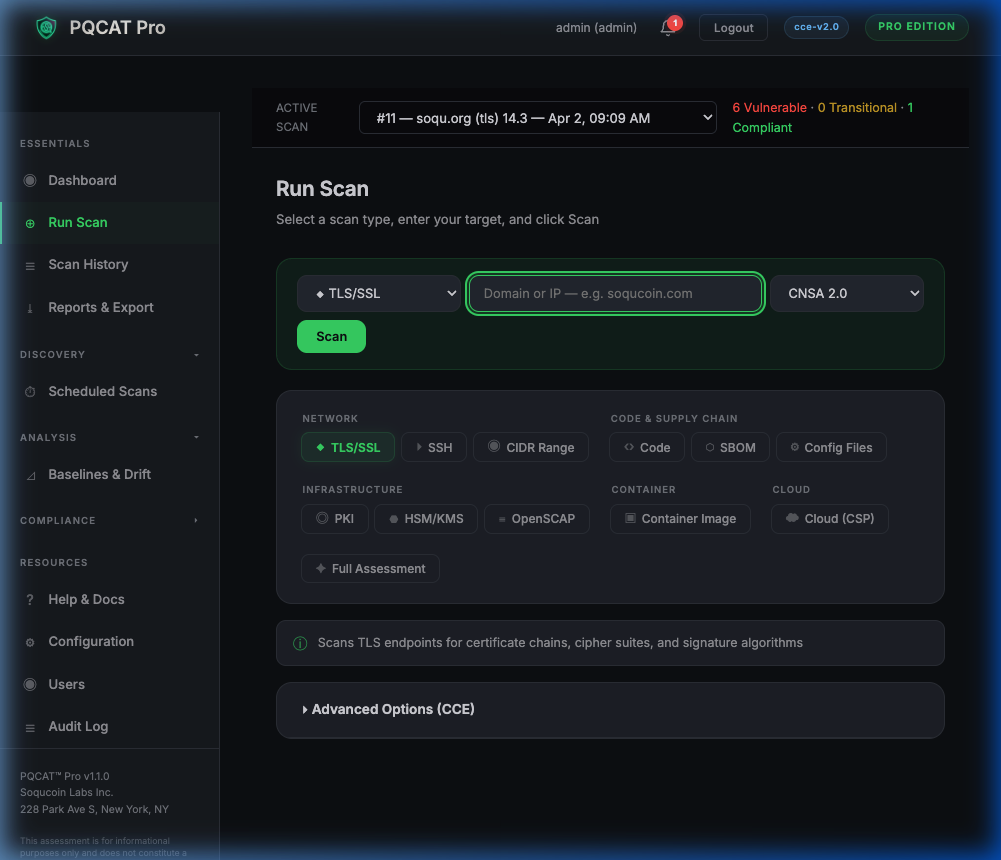
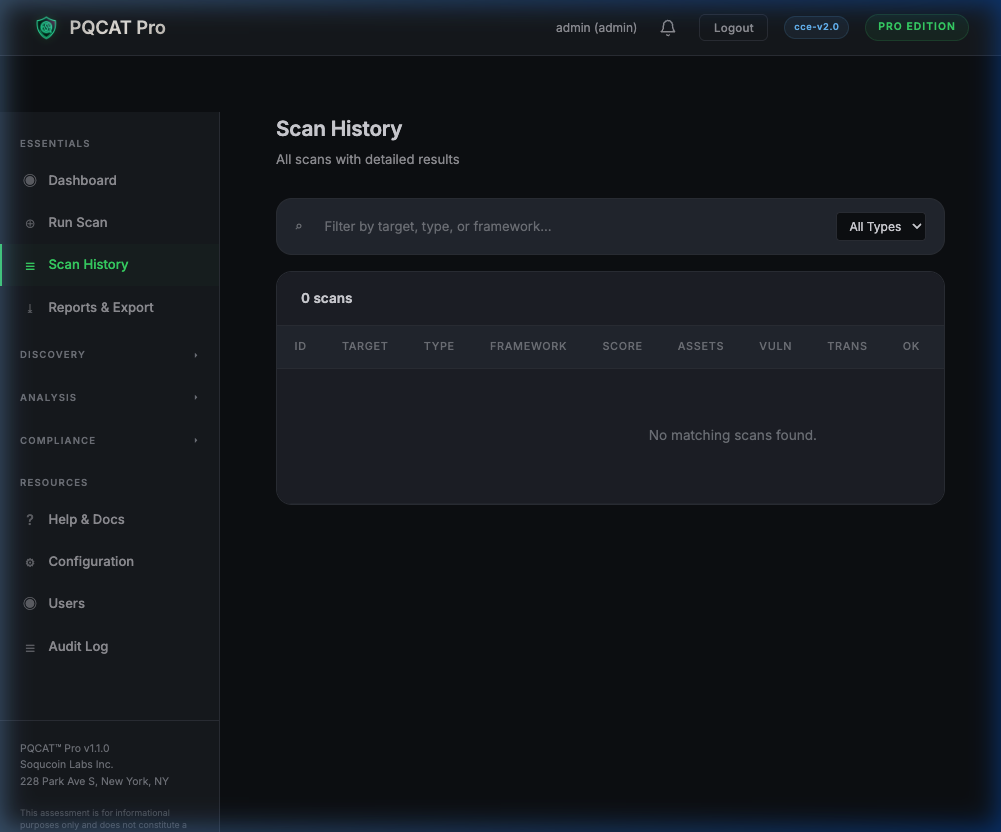
REST API, web dashboard, multi-user RBAC, SIEM forwarding, and executive reporting for SOC teams.
Scan AWS cloud-native cryptographic , KMS keys, ACM certificates, ALB/ELB TLS policies, S3 encryption, and IAM signing certificates.